Increase Revenue
Capture more earned revenue by boosting revenue cycle effectiveness through maximizing data quality in real-time and automatic information correction.
Reduce cost and improve efficiency
Raise staff productivity and eliminate 90% of the manual work via digitizing all processes, automating your specific workflows, and utilizing AI.
Maximize business potential
Track and improve business performance and operational processes via analytics-driven actionable insights and smart dashboards.
Delight providers and patients
Offer a digital experience that is modern and engaging, designed to make submitting orders and receiving results by providers effortless, and to provide patients with the responsiveness and transparency they expect.
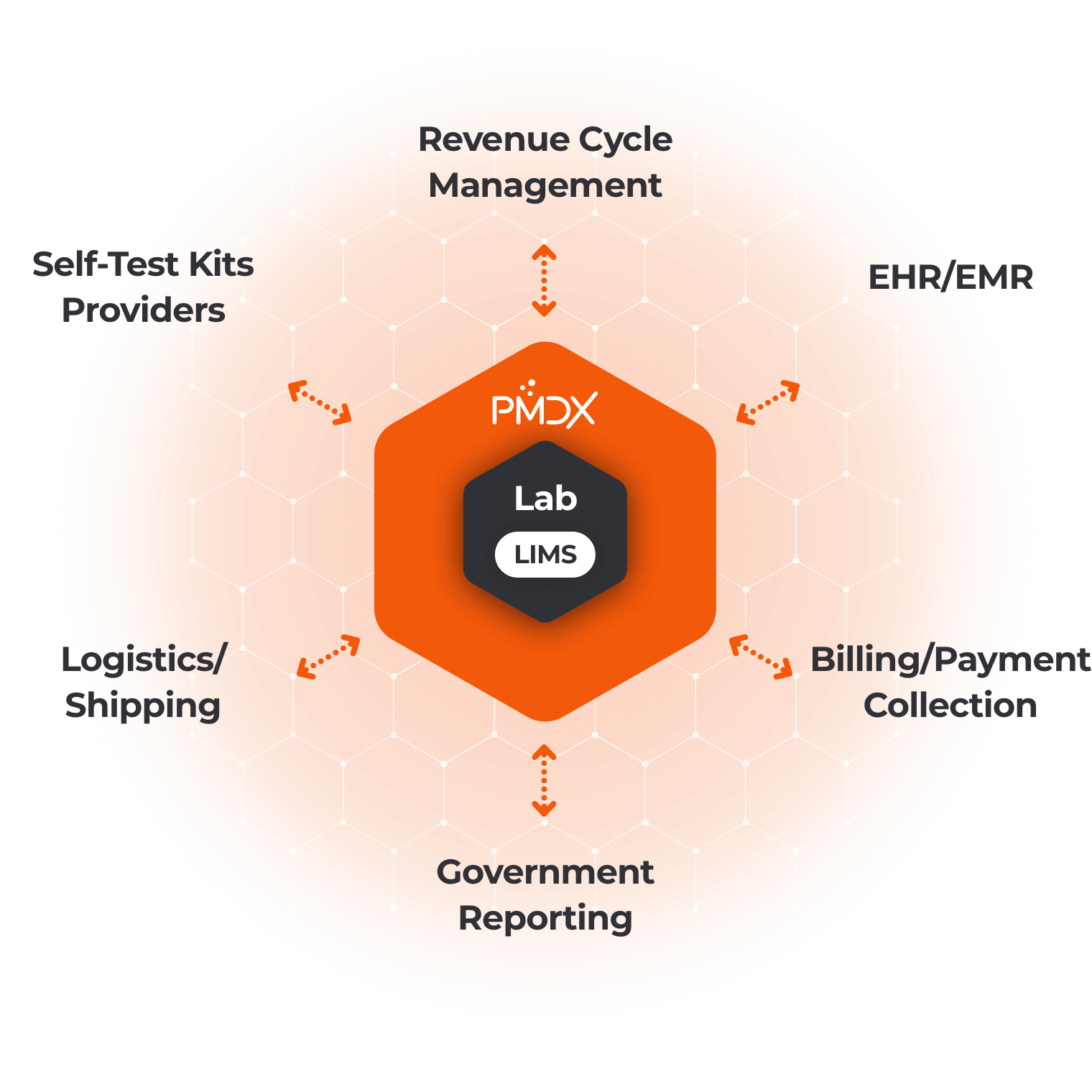
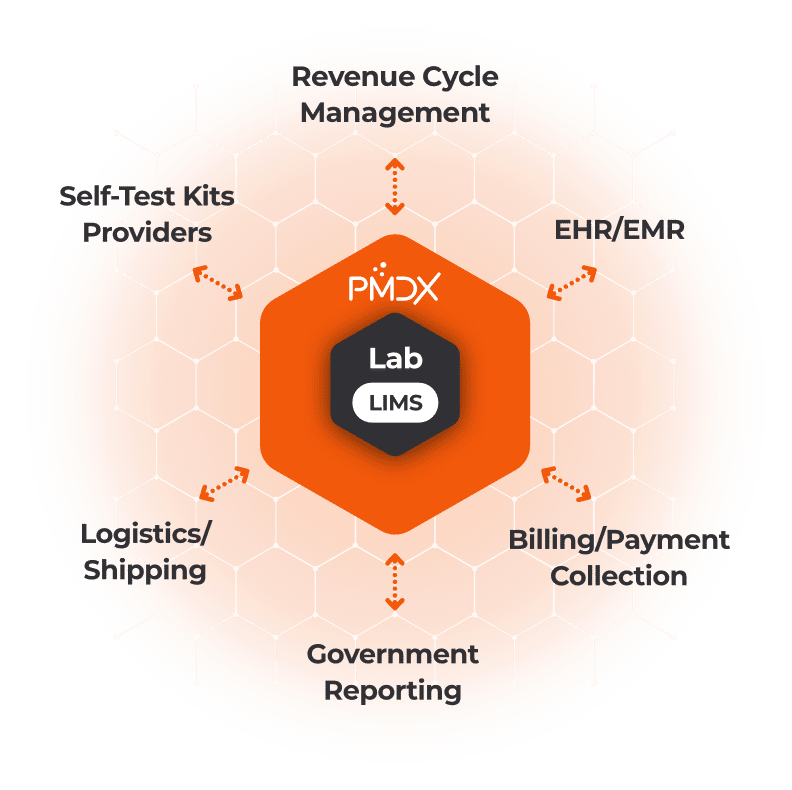
Connect and cooperate
Easily connect to all ecosystem partners and systems, such as LISs/LIMSs, providers’ and clinics’ EHRs, billing systems, payment gateways, data curation and augmentation sources, reference labs, self-test kit providers, and more.
Launch quickly and stay agile
Be live and running within days, regardless of your organization’s size, complexity, and test volume. Using the solution’s robust self-configuration tools, effortlessly create and adjust workflows, set up new test types, configure data collection journeys, manage automation rules, and more.